Introduction
In a world where online fraud and digital hacks are on the rise, it’s never been more important to verify that your customers are who they say they are.
Luckily, advancements in facial recognition software now enable streamlined biometric identification and authentication. For you, this means KYC and AML onboarding processes.
Harnessing the power of blockchain technology, the DynamicID from Verify 365 offers a secure and efficient way of verifying one’s identity and this is an example of just one of the benefits.
What is Biometric Facial Recognition?
Biometric identification technology encompasses software that identifies persons by their biological characteristics. For example, criminal investigations may use biometric fingerprint or DNA scanners, while high-tech security systems may involve iris scanning technology. Biometric facial recognition software identifies people from their facial features.
Most often, biometric facial recognition is used to automatically recognise a person from their face, a video, or an image. This is usually for biometric authentication, identification, or categorisation, however, Verify 365’s DynamicID risk engine allows for more.
DynamicID leverages NFC chip data and biometric scanning to quickly and accurately verify the identity of clients. When a client wants to verify their identity, they take a photo of their valid document such as a passport or driving licence. The app then scans the NFC chip data and the client’s biometric information, such as facial recognition, to verify their identity.
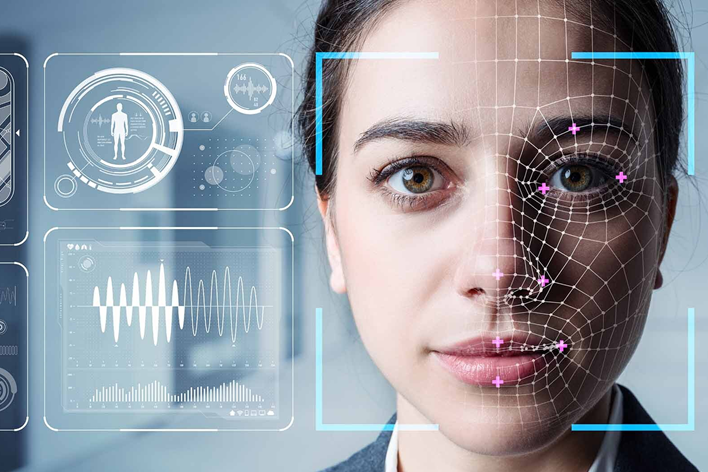
Facial recognition technology uses a visual pattern recognition process to match images or faces. It reconstructs a three-dimensional image from the information on a two-dimensional image and matches it to a person. The technology uses lighting, expressions, and poses to match the visual patterns between the two-dimensional image and the three-dimensional person. To complete this task, DynamicID biometric facial recognition technologies tend to deploy five modules: detection, normalisation, processing, feature extraction, and matching.
In addition to NFC chip data and biometric scanning, DynamicID also includes liveness checks in its capabilities. A liveness check is a process used to ensure that the person being verified is actually present and not using a fake or manipulated image, such as a photograph or a video. DynamicID uses advanced liveness detection algorithms to perform a real-time analysis of the client’s biometric data, ensuring that they are indeed physically present.
The DynamicID biometric risk engine uses advanced algorithms to analyse the biometric data and NFC chip data, comparing it against a database of known identities to determine if the client is who they claim to be. If the client’s identity is verified, a certificate is generated, which can be used as proof of identity.
DynamicID is designed to provide a secure and efficient solution for identity verification. By using NFC chip data and biometric scanning, it eliminates the need for physical identity documents and reduces the risk of fraud. The biometric risk engine also ensures that the client’s personal information is safe and secure, as it is stored on the blockchain and encrypted using state-of-the-art encryption methods.
How Does DynamicID Biometric Facial Recognition Work?
DynamicID biometric facial recognition technology works by using pattern matching software. Human bodies have ingrained patterns that are unique to each person (fingerprints, ear shapes, hand geometry, and so on). These are known as biometric modalities.
Facial recognition works by matching the biometric modalities in an image to a person or vice versa, or from an image to another image.
The facial recognition process is broken down into five steps:
- Detection
- Normalisation
- Processing
- Extraction
- Matching
Detection:
The face image detector locates human faces from an image, separating the face from a simple or complex background. This component of the technology divides ‘face’ and ‘non-face’ images to segment the face, its location, and its scale.
Normalisation:
Next, the face normalisation tool geometrically aligns the face using canonical coordinates. Harnessing facial landmarks, such as the eyes, ears, nose, mouth, and face outline, the normalisation process picks out the identifying facial features and their positioning.
Processing:
The face processing step is not always present in traditional facial recognition systems. However, in deep learning technologies, this tool will help to process the lighting and pose of the face in order to relay the two-dimensional image into a three-dimensional representation.
Extraction:
The extraction process pulls out facial features to differentiate between individuals. Using around 32 geometric and photometric points, this process modifies the pixels of features in an image into a vector representation (or vice versa).
Comparison:
The final step is the comparison stage. This is where a facial comparison software matches patterns from the image to databases to find the best match. Facial recognition software used for identification is often referred to as Automated Facial Recognition (AFR).
When comparing facial images to databases, AFR performs either closed-set or open-set identification. Closed-set identification is when a person is known to be in the database, therefore verifying and authenticating a person. This is the process used in KYC verification.
Open-set identification is when the person is not known to be in the database, as with crime database searches.
While most facial recognition software incorporates all of these stages, traditional and deep-learning systems differ in how the features are recognised.
In traditional biometric facial recognition technologies, the features are programmed by the human being designing the algorithms in the software. In a deep learning tool, the features that are extracted and compared are learned via the neural network. This neural network originally comprises a pool of subjects which are used to train the technology. This type of software expands its neural network and breadth of ‘knowledge’ with the more faces and features it analyses.
While biometric facial recognition technology works by completing the steps above, the way in which it compares faces depends on the task in hand. Most often, facial recognition is used to identify, authenticate, or classify a person.
In the case of identification, the software will match the unique modalities of a person against many other faces to determine the individual’s identity. For verification purposes, the software will attempt to match a person’s facial features to only one person in the hope of verifying that a person is who they claim to be.
When it comes to categorisation, the software matches a person’s features to a specific group to determine if a person belongs to this group (usually based on age, race, sex, etc.).
Challenges of Biometric Facial Recognition
While biometric facial recognition can be profoundly useful for identifying, verifying, and classifying human beings, it can also be easily misused. A rapidly accelerating technology, facial recognition software comes loaded with heavy warnings as an ethical concern bubbles to the surface. Selecting the wrong digital identification and verification system for your company may lead to these challenges.
Privacy and Security
One of the major issues with biometric facial recognition software is the large-scale collection of personal biometric data. Not only is this practice morally questionable, but it also poses intense issues with data security. With the GDPR and similar legislation cracking down on data ownership, usage, and distribution, biometric facial recognition technology has received a lot of heat. While the technology itself may not breach usage rights, hacks and leaks lead to sensitive data being made public.
Due to the fragility of this situation and to the obvious potential for misuse, the EU (in accordance with the GDPR) is making a stand on facial recognition technology by laying down strong limits as to usage rights of such data.
The first GDPR fine related to facial recognition technology was issued back in 2019. The Swedish Data Protection Authority (DAP) recently fined a Swedish school that was using AFR to monitor attendance. The DPA found the school to be processing personal data more than was necessary and without implementing effective data protection mechanisms. The DPA also claimed that the school did not have prior consent and had no legal basis for collecting such data.
Misidentification
The accuracy of biometric facial recognition technology is highly dependent on the technology used and how it is implemented. This can result in misidentifications, which can have serious consequences. For example, the Welsh police’s internal facial recognition software misidentified 2,300 individuals as criminals, while the Metropolitan Police in London has been found to have an error rate of 81% in their face recognition service.
Misidentification by facial recognition systems is a major problem when it comes to fraud. Face spoofing attacks, where fraudulent individuals use photographs or pre-recorded videos to fool the system, can lead to unauthorised access to bank or computer accounts. Research has even shown that facial recognition software, such as Windows, can be bypassed using a printed picture.
Bias
Bias is one of the key issues with biometric facial recognition technology. In traditional systems, the programmer determines the features that the software is able to recognise, and if they don’t provide a diverse enough set, the software may not be able to accurately recognise all individuals.
This same problem is present in deep-learning facial recognition software. If the original data used to train the software is not diverse enough, it will result in bias in what the software can detect.
Given that the majority of programmers in our society are white males, this has resulted in a bias toward white males in facial recognition software. The “Gender Shades” project found that women of color are the most vulnerable group to gender misclassification, with a misidentification rate 34.4% higher for dark-skinned women compared to light-skinned men.
This has major implications for racial prejudice, particularly in the criminal justice system. In a study of Amazon’s facial recognition tool, “Rekognition,” racial bias was evident. The system returned 28 false positives when comparing 535 members of US Congress with a database of 25,000 arrest photos. Although a 5% error rate may seem acceptable, 39% of these false matches were people of color, even though people of color only made up 20% of the original group. This demonstrates a clear racial bias in this particular facial recognition software.
Real-World Use Cases of Biometric Facial Recognition
Biometric facial recognition technology is becoming a crucial part of various industries such as security, authentication, and analysis. This technology is being utilised in imaginative ways to improve and streamline operations.
Criminal justice systems are using biometric facial recognition to locate criminals and escapees, locate missing individuals and reunite them with their families, and combat human trafficking by scanning online advertisements. It is also being used as a tool to prevent fraud in financial institutions and banks.
In e-commerce, biometric facial recognition technology is being used to enhance customer service. For instance, Beijing KFC is experimenting with the system to recall customer orders by using their facial biometrics, which then suggests their previous order during their next visit. AliPay has launched the first-ever facial recognition payment system, which not only speeds up the payment process but also adds extra security.
Transportation companies are implementing biometric facial recognition technology to minimize wait times for customers, such as Delta Air Lines’ trial of facial recognition scans in airports. The healthcare industry is using the technology for patient monitoring and sentiment analysis, detecting genetic disorders, and preventing fraud.
In the education sector, facial recognition technology is still being considered for attendance tracking, despite data protection concerns. Schools are also looking into the technology to prevent bullying. Facial recognition software is being developed to aid blind individuals in social situations by recognizing facial expressions.
How is Verify 365 Leveraging Biometric Facial Recognition?
Verify 365 are using biometric facial recognition technology to help regulated sectors, such as law firms and financial institutions, identify and verify their clients, while also helping those users identify themselves more easily online.
Verify 365’s facial recognition technology, DynamicID, automatically identifies and verifies users by matching their image to their official documentation and existing databases. This will highlight any fraudsters, Politically Exposed Persons, or individuals subject to sanctions. This speeds up and cuts costs in your KYC process while ensuring complete AML compliance.
What makes DynamicID application of facial recognition so promising is that we combine it with various identification and verification procedures to increase security and accuracy. Where other applications of facial recognition softwares only offer a single layer of verification, DynamicID guarantees security with our multidimensional authentication process.
Our biometric facial recognition system is teamed with Optimal Character Recognition and Biometric Liveness Detection. This creates a multilayered approach that verifies users most accurately, safeguarding against face spoofing and misidentification.
Not only does this speed up the process of KYC for many organisations, but it also enhances precision and removes human error in the identification and authentication process.
Why switch to Verify 365?
Harnessing biometric facial recognition tools for identification and verification can help to speed up your KYC processes and ensure that you are up-to-date with AML compliance. However, deploying the wrong software can leave you facing issues of data security and misidentification.
Thankfully, Verify 365’s automated multilayered verification platform provides a biometric identity authentication technology that overcomes these challenges. Combining biometric facial recognition with liveness detection, Verify 365’S comprehensive client onboarding solution offers top-notch accuracy for speedier, more cost-effective verification. Simultaneously, our data storage architecture keeps all biometric data firmly locked away with the user.
For your company, this means full data security and AML compliance, with sleeker KYC processes. For your customers, this means smoother onboarding and security they can trust.
If you’re looking for a robust biometric identification and authentication solution to streamline your KYC and AML processes, contact Verify 365 today to learn more.